Phishing: Why Modern Security Solutions Are Essential
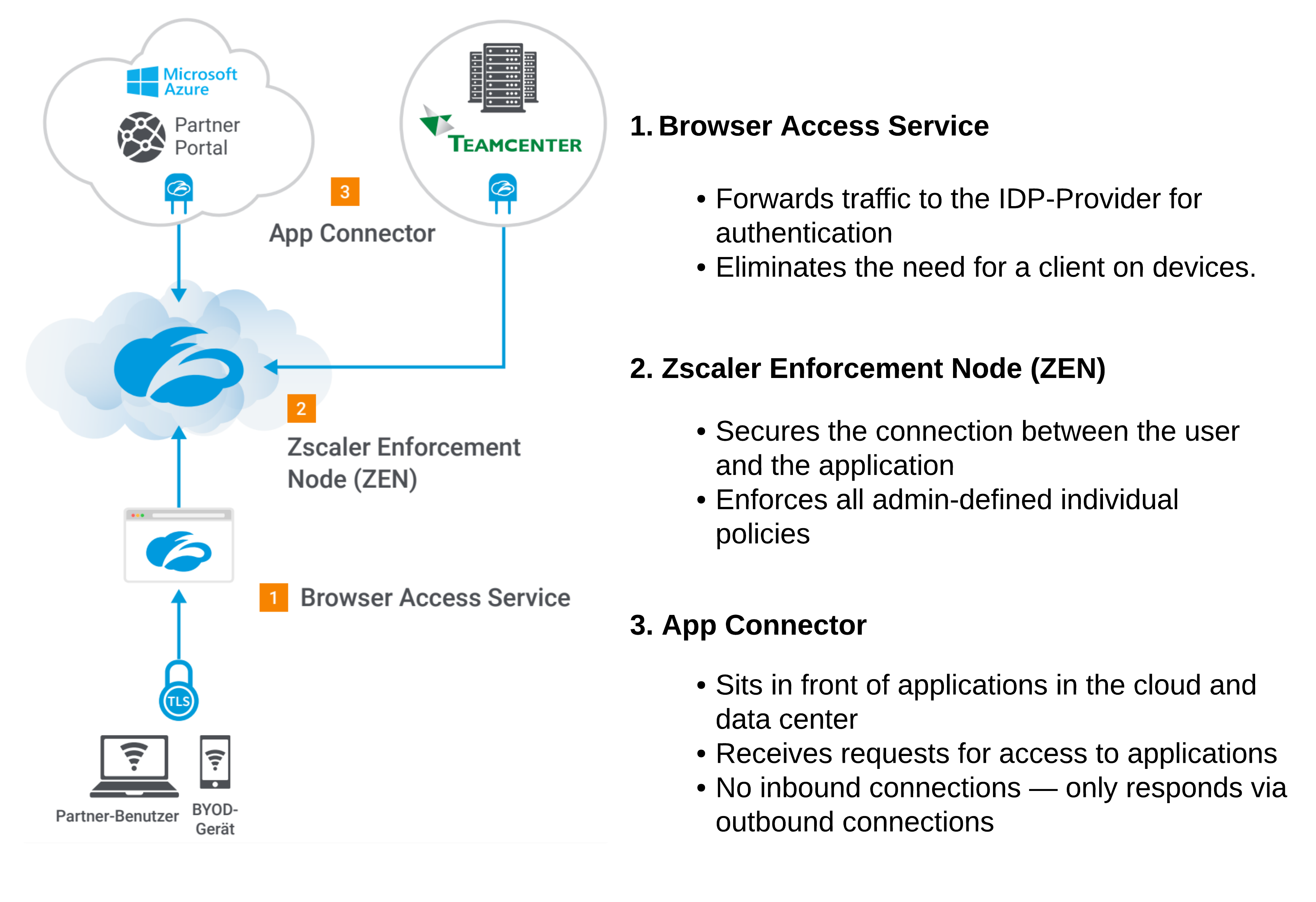
Phishing attacks are becoming increasingly sophisticated and dangerous. Find out why modern security solutions are essential for companies to protect themselves against these threats.
Use text and images to tell your company’s story. Explain what makes your product or service extraordinary.